
In the recent couple of days/weeks, we have been noticing a lot more spam e-mails targeting Gmail, Outlook and Hotmail addresses. We received multiple messages a day. The spam collection mailboxes across different public domains (mainly Gmail, Hotmail, Outlook, ...) all got heavily targeted, 5+ emails a day, with 100+ a week blocked by SPAM filters.
A lot of these emails originate from the following countries (the mail server with CrowdSec, Rspamd and ClamAV gave these alerts.
You might receive a message from Colruyt about winning a price for the loyalty program of Colruyt. That program does not actually exist. The mail coming is from marketing@nzpanels.ug.nz). Other messages we have been seeing, are failed delivery messages with a non-standard subject in the emails from Gamma, Bpost, Media Markt. These e-mails are coming from: info.go7kw4Rx3@la86m.co.uk, no_reply@midasedu.in, employers@christiansuper.com.au...)


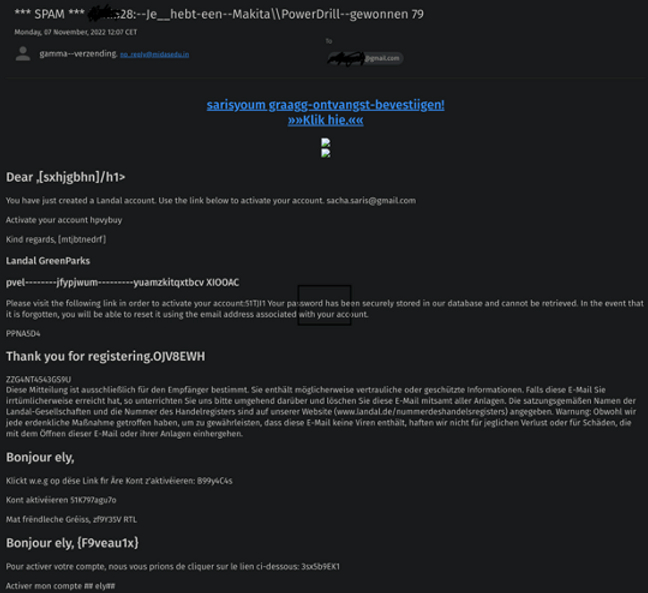
The main take is to always check if the email is coming from the correct domain linked to the company trying to reach you. A lot of the times e-mail domains look almost legit, switching an "a" for an "o" and other small changes that easily go unnoticed when clicking and following an URL.
Religious domains are an easy target for hackers since they don't use advanced techniques to mitigate attacks and are therefore more prone to attacks (hobbyist websites). The general public that is subscribed to those type of religious emails tends to be, for a lack of a better description, people easily susceptible to believing what they receive (older people, non-technical users...). If you never subscribed to religious emails / domains, those emails should be ignored as they are 9/10 malicious (mark as spam/Junk and delete to train the SPAM filter to block similar messages or all messages from that domain respectively).
The same goes for smaller educational institutions around the world. You should never blindly trust domains that have a mix of random letters and numbers, since those are very cheap (sometimes free) and actively used by malicious actors to send out Spam and Junk.
Perhaps we can include solutions that might: train the workforce for safe email etiquette, create insight and secure your environment (knownbe4, O365 security, Hornet Security -full solution or Veeam - backup solution, if we ever want to go the full secure M365 route).
Looking at the maturity of one of our current clients, they actually use external services to protect O365 users, since they do not blindly trust the MS services like a lot of other companies do. Larger enterprises do not blindly trust the MS solutions, and choose to harden their cloud environments with external tools.
Risks when opening links / attachments from spam mails:
- You get redirected to a fake MS logon Page, they steal your credentials and take over your O365 account. Currently these attacks are getting so advanced that they proxy your requests as a legitimate request to O365. Then they proxy MFA prompts and gain access to MFA enabled accounts for further use
- Malicious software or scripts are run on the device to exfiltrate information from your device
- Ransomware